|
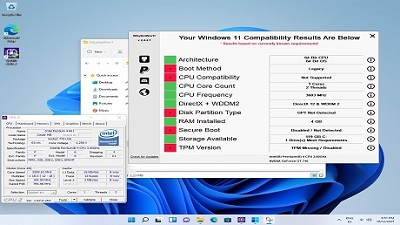
Windows 11 has become one of the most divisive and confusing OS releases in recent history, despite Microsoft's efforts to announce and detail the system's capabilities, requirements, and differences relative to Windows 10. While Microsoft has accompanied communications on Windows 11 with stringent system requirements, there are already numerous ways to circumvent hardware limitations floating through the internet. The latest such experiment, carried out by user @Carlos_SM1995 (via Notebookcheck), actually managed to install and run the OS on supposedly - according to Microsoft - incompatible hardware. What is this mysterious chip that can actually run Microsoft's latest OS? It's an all-powerful, single-core Pentium 4 661 CPU from 2006. It does feature Hyper-Threading, though. To be fair to Microsoft, the system requirements refer to the hardware configurations that can run Windows 11 out of the box, and which can sustain all of its features - including security-focused ones, which were the basis for the Trusted Platform Module (TPM) requirement, and others. It certainly sounds fair to say that Microsoft would finalize its system requirements based on users taking advantage of all of the OS' features - and it really wouldn't make much sense to take any other course of action. Some of Windows 11 security features require specific hardware implementations to run smoothly when they're actually active - but naturally, should those features be disabled, the performance hit doesn't actually register for the end-user. As such, we would say that the fault lies not on Microsoft; as it is one thing to run the OS as intended by the company. The other is to find ways to skirt some of those requirements by disabling features that one will not use - such as TPM, Secure Boot, or Virtualization-Based Security (VBS) features. This is exactly what was done to run this particular Windows 11 OS build and the system even receives updates via the integrated Windows Update functionality, as you can see in the video below. What Microsoft could have done, of course, is clarify which features can be disabled by users in order to achieve broader backward compatibility. But again, it doesn't seem like such a great idea for Microsoft to ship Windows 11 with security-facing features and then tell users how to disable them - that's just not a good IT security practice, period. There are natural risks when disabling OS features - especially security-centric ones, and Microsoft is playing it safe. Yet ultimately, this proves that users can still have control over what hardware they run their Windows 11 build - even if it just so happens that the hardware is a Pentium 4 from 2006. Follow this and more on OUR FORUM. Microsoft Corp., which has faced pressure from employees and shareholders over contracts with governments and law enforcement agencies, agreed to commission an independent human rights review of some of those deals. The move came in response to a June filing of a shareholder proposal asking the company to evaluate how well it sticks to its human rights statement and related policies. Microsoft committed to a review of any human rights impacts that its products have on those including communities of Black, Indigenous, and People of Color in contracts for police, immigration enforcement, and unspecified other government agencies, according to correspondence from the company viewed by Bloomberg. Microsoft pledged to publish the report next year, and the shareholders, who include faith-based investors like Religious of the Sacred Heart of Mary, have withdrawn their proposal ahead of Microsoft’s annual shareholder meeting next month. Microsoft spokesman Frank Shaw confirmed the company will undertake the review. “In response to shareholder requests, Microsoft Corp. will commission an independent, third-party assessment to identify, understand, assess, and address actual or potential adverse human rights impacts of the company’s products and services and business relationships with regard to law enforcement, immigration enforcement, and other government contracts. The assessment will include consultation with BIPOC communities, including immigrants, and other groups representing communities most impacted by Microsoft’s surveillance products, law enforcement, and government contracts,” the company said in a statement. As a government, military and police contracts have become targets of scrutiny and activism, Microsoft employees have circulated letters demanding the company abandons a deal to build versions of its HoloLens augmented reality headsets for the U.S. Army as well raising concerns about business with U.S. Immigration and Customs Enforcement. Chief Executive Officer Satya Nadella has stood behind software sales to the U.S. military, but paused selling facial recognition technology to police departments, although the company sells other programs to law enforcement. The California-based religious order agreed to lead the shareholder proposal because it wanted to make sure the company’s products don’t “cause human rights harms, including perpetuating systemic racial inequities,” Sister Joanne Safian, said in a statement. Microsoft told the investors the review will be conducted by the law firm Foley Hoag LLP. The proposal was filed by Investor Advocates for Social Justice, a nonprofit representing faith-based institutional investors. Microsoft didn’t specify which contracts will be examined, but shareholders “expect” it will include what the group said are about 16 active contracts with ICE and U.S. Customs and Border Protection. “This will be an ambitious and complicated process and we’re certainly putting our faith in Microsoft and Foley Hoag to be conscientious,” said Michael Connor, executive director of Open MIC, a nonprofit shareholder advocacy organization that worked with IASJ on the proposal. “They’re asking for input from affected rights holders, which was a very big request on our part and they agreed to that.” Human rights concerns have been raised by shareholders in areas related to labor and in the apparel industry around manufacturing conditions but are newer to the technology companies, he said. Open MIC has also made similar requests of Amazon.com Inc., related to its facial recognition technology, as well as Apple Inc., Facebook Inc., and Alphabet Inc., without a positive response from the companies or a win at shareholder meetings, Connor said. Follow this and more by visiting OUR FORUM. More than $1.4 million has been stolen from victims through a cryptocurrency-related scam perpetrated through dating apps. Sophos has released a new report this week about a dating app scam that led to the theft of millions of dollars from people on Tinder, Bumble, Grindr, Facebook Dating, and similar apps. After gaining their trust in these dating apps, scammers convinced victims to download fake crypto apps, where they duped them into investing money before freezing the accounts. The scammers were somehow able to easily game Apple's Developer Enterprise program -- and the Apple Enterprise/Corporate Signature -- to distribute these fraudulent crypto apps, which were masquerading as Binance and other legitimate brands. Sophos said its threat hunters observed the scammers abusing Apple's Enterprise Signature to manage victims' devices remotely. Apple did not respond to requests for comment. Sophos also contacted Apple about the issue and did not get a response. Named "CryptoRom," according to Sophos researchers Jagadeesh Chandraiah and Xinran Wu, the scam has led to at least $1.4 million being stolen from victims in the US and EU. In their report, the two say that the attackers moved beyond going after victims in Asia and instead are now targeting people in Europe and the US. Sophos researchers even managed to find a Bitcoin wallet that was being controlled by the attacker's thanks to one victim, who shared the address he initially sent the money to before being shut out. Chandraiah said the CryptoRom scam relies heavily on social engineering at almost every stage. Victims came to Sophos to discuss the scam and the researchers found other reports of people being taken advantage of. "First, the attackers post convincing fake profiles on legitimate dating sites. Once they've made contact with a target, the attackers suggest continuing the conversation on a messaging platform," Chandraiah said. "They then try to persuade the target to install and invest in a fake cryptocurrency trading app. At first, the returns look very good but if the victim asks for their money back or tries to access the funds, they are refused and the money is lost. Our research shows that the attackers are making millions of dollars with this scam." Victims are initially contacted on apps like Bumble, Tinder, Facebook dating, and Grindr before the conversation is moved to other messaging apps. From there, the conversation is steered toward getting victims to install fake trading applications onto their devices. Once a victim is drawn in, they are asked to invest a small amount before being locked out of accounts if they demand their money back. The attack is two-pronged, giving cybercriminals the ability to steal money from victims and gain access to their iPhones. According to Wu and Chandraiah, the attackers are able to use "Enterprise Signature" -- a system built for software developers that assists enterprises with pre-test new iOS applications with selected iPhone users before they submit them to the official Apple App Store for review and approval. "With the functionality of the Enterprise Signature system, attackers can target larger groups of iPhone users with their fake crypto-trading apps and gain remote management control over their devices. This means the attackers could potentially do more than just steal cryptocurrency investments from victims. They could also, for instance, collect personal data, add and remove accounts, and install and manage apps for other malicious purposes," the researchers said. Chandraiah added that until recently, criminal operators mainly distributed the fake crypto apps through fake websites that resemble a trusted bank or the Apple App Store. "The addition of the iOS enterprise developer system introduces further risk for victims because they could be handing the attackers the rights to their device and the ability to steal their personal data," Chandraiah said. "To avoid falling victim to these types of scams, iPhone users should only install apps from Apple's App Store. The golden rule is that if something seems risky or too good to be true – such as someone you barely know telling you about some 'great' online investment scheme that will deliver a big profit – then sadly, it probably is." Follow this thread on OUR FORUM |
Latest Articles
|